Tag: Hacker

Ransomware Is A Billion Dollar Game Of Cat And Mouse
Cyber security is a never-ending game of cat and mouse between criminals and those offering some form of protection, which is why we can never rest on ...

The Top 5 Most Realistic Hacker Movies Ever Made
For a long time, Hollywood has followed a tradition of taking mundane, everyday tasks and highly dramatizing and simplifying them to create an engagin ...
![Hacker Profiles – The Bad Guys Of Online Security [Infographic] Hacker Profiles – The Bad Guys Of Online Security [Infographic]](https://bitrebels.com/wp-content/uploads/2016/07/hacker-profiles-bad-online-security-infographic.jpg)
Hacker Profiles – The Bad Guys Of Online Security [Infographic]
Not a single Internet user doesn't know that a certain evil is at large on the Internet. They are called hackers and sometimes cause havoc to secure s ...
![What A Phishing Email Looks Like And How To Detect One [Infographic] What A Phishing Email Looks Like And How To Detect One [Infographic]](https://bitrebels.com/wp-content/uploads/2013/08/how-to-detect-phishing-email.jpg)
What A Phishing Email Looks Like And How To Detect One [Infographic]
If you are on your computer all day, it would probably be hard for a scammer to entangle you in the web of a phishing email. I've had my identity stol ...
![How Hackable Is Your Life & Everyday Tech? [Infographic] How Hackable Is Your Life & Everyday Tech? [Infographic]](https://bitrebels.com/wp-content/uploads/2013/08/how-hackable-are-you-infographic.jpg)
How Hackable Is Your Life & Everyday Tech? [Infographic]
With the increased amount of technology in our lives, the possibility of identifying theft is rising along with it. Whether or not we will get hacked ...
![Are You An Easy Hacker Target? [Infographic] Are You An Easy Hacker Target? [Infographic]](https://bitrebels.com/wp-content/uploads/2013/04/hacker-target-victim-statistics-infogrphic.jpg)
Are You An Easy Hacker Target? [Infographic]
How much do you know about computer security? Did you know that without a firewall or anti virus protection, your computer is like an open book for pr ...

5 Fresh Faces Of Strategic SEO Who You Probably Don’t Know
SEO is a dynamic industry, and that's one of the things that makes it so special. Search Engine Optimization picked up its spark in late 90's when Bru ...
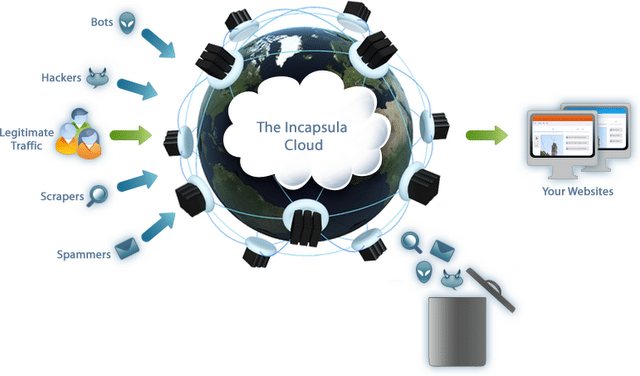
Incapsula: Website Security Protection To Keep Cyber Cyclopee Out
Recently, I wrote a bit of a rant about the ins and outs of protecting your website from Zombie hackers, malicious code snakes and spammers in Keep Bl ...
![Password Strength: How Strong Is Your Password? [Infographic] Password Strength: How Strong Is Your Password? [Infographic]](https://bitrebels.com/wp-content/uploads/2012/10/password-strength-security-breach-infographic.jpeg)
Password Strength: How Strong Is Your Password? [Infographic]
Internet security has always been a continuously evolving issue we've all had to deal with at one point or another. There are new and stronger securit ...

Cloud Storage: Getting Hacked Might Be More Likely Than You Think
Feeling secure in this lovely, shiny new online world of the cloud? Spare a thought for Wired Journalist Mat Honan who had his iCloud account breached ...

OS X Inspired Dishes: Perfect For Late Night Snacking Hackers
If you are like me, and you don't need a lot of sleep, you know that in the middle of the night you sometimes get the munchies, right? I usually stay ...
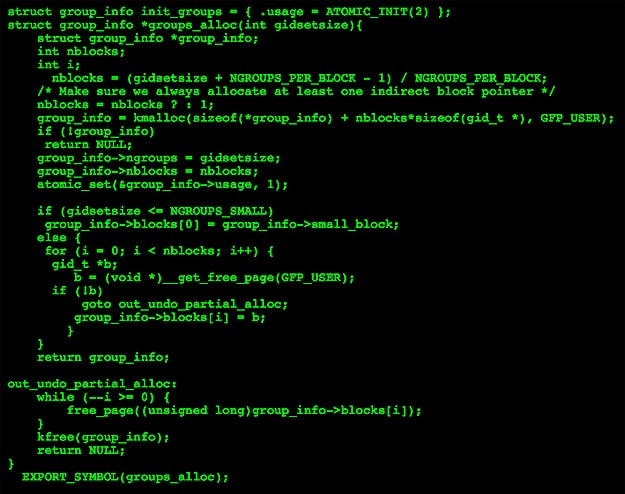
How To: Be A Hacker (Or Just Look Like One)
Have you ever wondered what a computer hacker looks like? You might be surprised to know. If you haven't had much experience with all things related t ...
![Twitter Malware: A Complete Timeline [Infographic] Twitter Malware: A Complete Timeline [Infographic]](https://bitrebels.com/wp-content/uploads/2011/04/Twitter-Malware-Complete-Timeline-Infographic-1.jpg)
Twitter Malware: A Complete Timeline [Infographic]
You are using Twitter, right? If you have used the social networking service for a while, you are well aware of the hiccups it has had through its exi ...
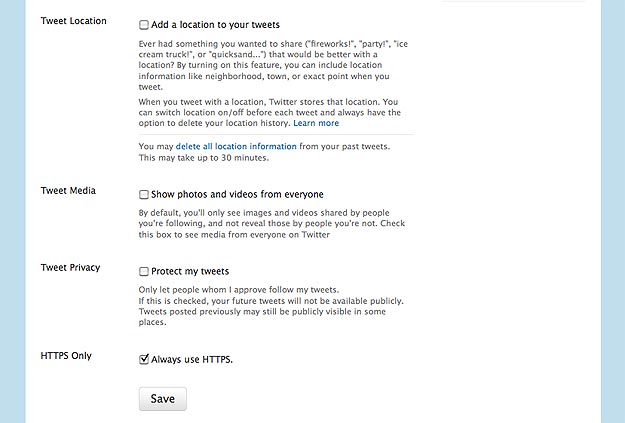
The Twitter HTTPS Setting In Plain English
We've all seen the tweets over the past few days about the new "HTTPS Only" checkbox in our settings menu in Twitter, but a lot of people still don't ...

Protect Your Password With Help From A Geeky Stripper
As we all know, computer hackers are getting better at what they do each day, thus becoming a daily annoyance that many of us think about. Just this ...